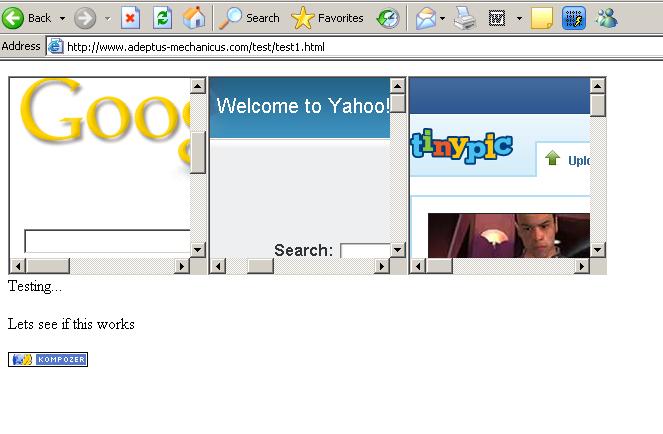
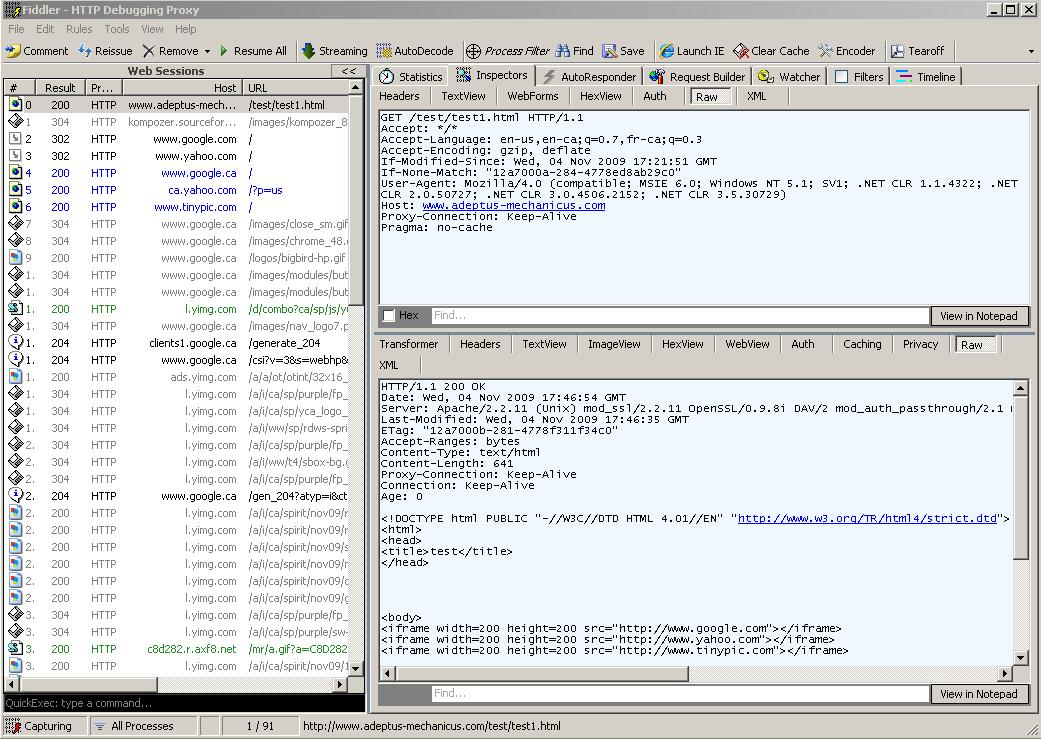
| <iframe width=200
height=200 src="http://www.google.com"></iframe> <iframe width=200 height=200 src="http://www.yahoo.com"></iframe> <iframe width=200 height=200 src="http://www.tinypic.com"></iframe> |
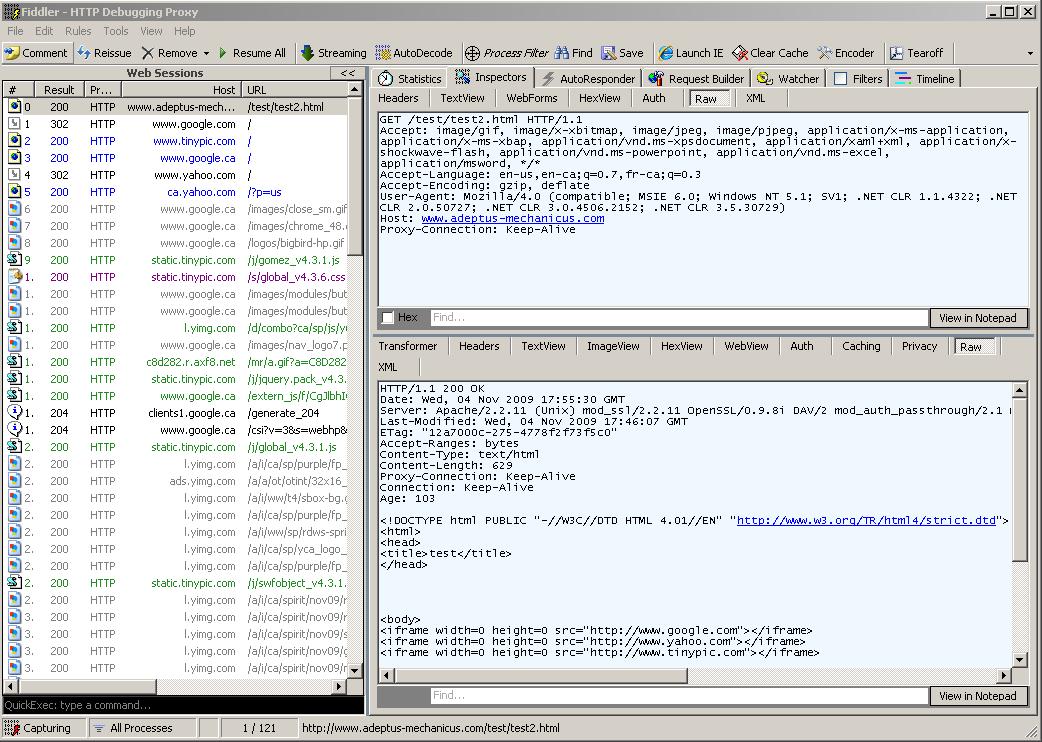
| <iframe width=0
height=0 src="http://www.google.com"></iframe> <iframe width=0 height=0 src="http://www.yahoo.com"></iframe> <iframe width=0 height=0 src="http://www.tinypic.com"></iframe> |